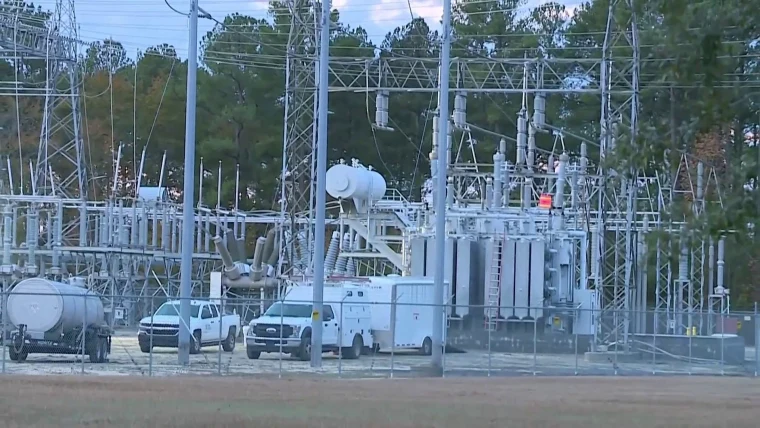
The recent attack on two North Carolina substations that cut power to thousands of people has raised concerns about security standards for the country’s electric grid and its numerous power stations, which have faced greater threats in recent years.
Outside of weather, suspected and confirmed physical attacks on electric grid infrastructure have been the largest cause of electrical disturbance events since 2014 when, in response to an attack in California the year before, private companies that run power stations were required to increase security standards, according to an NBC News analysis of public Department of Energy reports.
Nearly 600 electric emergency incidents and disturbances were caused by suspected and confirmed physical attacks and vandalism on the electric grid in those nine years, the reports show. There have been 106 attack or vandalism incidents from January through August 2022, which is the latest the Energy Department data tracks. Among the years reviewed by NBC News, 2022 is the first that reached triple digits and it only contains eight months of data.
The incidents, which are self-reported by power companies to the federal government, provide little to no detail about what occurred. But experts said they can range from theft of copper wire to planned assaults aimed at causing power disruptions, as is what is suspected to have happened in North Carolina.
“The significance of this outage in North Carolina in the middle of a really cold winter should not be underappreciated — it’s a huge deal,” said Neil Chatterjee, who served as chairman of the Federal Energy Regulatory Commission, or FERC, during the Trump administration. “We have to be cognizant of this and take physical security and cybersecurity seriously and there are things we can do in terms of standards and other approaches to harden and protect our critical energy infrastructure.”
Duke Energy restored power to all of its North Carolina customers Wednesday evening, four days after 45,000 customers were left in the dark after what officials have said was an intentional and coordinated attack on two substations in Moore County. Moore County Sheriff Ronnie Fields has said a motive for the attack is not known. It is also not clear what kind of protective measures were in place to prevent such an assault.
Jeff Brooks, a spokesman for Duke Energy, declined to provide specifics about the sites’ security measures but described the company’s security approach as “robust.”
“We have multiple layers of protection on our critical systems on the grid that help us to monitor and then respond when we have disruptions,” he said. “And so what we’re doing now is certainly focused on the restoration activity, but there will certainly be lessons learned from this that we will incorporate into our plans going forward.”
In response to the attack, a senior Department of Energy official said the agency convened a call on Monday that included Deputy Secretary of Energy David Turk, 30 CEOs from across the electricity sector, officials from Duke Energy and officials and investigators from the FBI, Department of Homeland Security, the White House and the National Security Council.
They discussed the attack and industry executives were told to be on alert and report any and all incidents that could be considered threatening.
“Until we start to connect some of the dots, we really do need to see: Where is this trending? What is going on?” the official said. “There was a real call out to say we need to go ahead and share that information while we also need to remain vigilant.”
The current standard was adopted in 2014 and requires power companies to create risk, threat and vulnerability assessments as well as a physical security plan for each station, all of which must be verified by a third party. It does not require them to pursue concrete or specific security measures at each site, however.
Adrienne Lotto, the senior vice president of grid security, technical and operations services at American Public Power Association, an advocacy group for power companies, said that the current standard works well because it is tailored to the specific risks at each site. She added that the utility sector has responded to the threats from a best practice perspective as well.
“Utilizing a risk-based approach, the sector tends to put, and rightly so, focus on those assets that have high impact or high risk to the bulk electric system,” she said.
But others don’t believe the current standard works well. Critics said they believe it is a vague set of rules that gives electric utility companies a great degree of leeway, rather than creating required, enforceable security measures.
Jon Wellinghoff, who was appointed chairman of FERC during the Obama administration, said the standards are “extremely vague” and “are not prescriptive,” as they do not require things like block walls or cameras.
“They simply say the companies have to identify what parts of their infrastructure are critical and each utility then makes that decision as to what parts of their infrastructure they want to put under the standards,” he said. “Then they have to create a plan to protect them and that plan can basically be anything that complies with the broad, vague outline of the standards.”
The senior Department of Energy official said that the North Carolina substation was not considered high impact, as it was not believed that damage to it would have caused an outsized effect.
“This was a low-impact substation, and therefore it has a different set of requirements when it comes to its physical security measures that it would employ,” the official said. “We are going to be working with Duke to really understand and assess the situation in terms of what security measures were in place and that’s going to inform the dialogue in terms of what we could change.”
Security standards last went through a major change after a coordinated firearm attack at a transmission substation outside San Jose, California, in 2013 raised concerns of a massive weakness in the U.S. electric system.
Those who coordinated the assault, known as the Metcalf sniper attack, remain at large. They created multiple firing positions and cut communications from the power station before firing upon 17 transformers, threatening a major blackout. PG&E, the power company, was able to reroute power to affected areas, but the attack could have caused an energy outage that would have included all of Silicon Valley, said Wellinghoff, who was chairman of FERC at the time.
Those who want a new security standard said there remain significant bureaucratic headwinds against such a proposal.
After the Northeast blackout in 2003, Congress passed the Energy Policy Act of 2005. That law had federal regulators turn to an “electric reliability organization” to develop and enforce reliability standards for the country’s transmission networks. The view is that the industry’s expertise would lend itself to creating strong reliability standards, while federal regulator FERC would approve the standards that organization creates.
Since 2006, the North American Electric Reliability Corporation has overseen the task of creating reliability standards, but critics say this process has effectively allowed the industry to make its own rules and sapped any power from FERC to act as a regulator.
The North American Electric Reliability Corporation, a nonprofit originally created by the electricity industry, said it created security requirements based on risk, rather than a one-size-fits-all approach.
“The assets in North Carolina were not individually deemed critical to the grid, and the recent attack did not create an uncontrolled or cascading outage, which is what the standards are designed to protect from,” said Kimberly Mielcarek, a spokesperson for the group. “However, this does raise the question of the need to review an event that impacts several non-critical assets that collectively can have impact beyond any single asset failure.”
Mielcarek added that expertise from the industry is the best way “to ensure our standards are technically sound and don’t cause unintended consequences on the grid.” FERC, she noted, can direct the organization to draft a standard if it deems it necessary.
For those who want greater action, however, the only route forward could be through an act of Congress, Wellinghoff said.
“Encouraging people to do things doesn’t get it done,” he said. “You have to give somebody the authority to actually do something, you have to give somebody authority to write a regulation, put it in place and require it to be implemented and to oversee it and enforce it.”
But Chatterjee said he was unsure whether a significant standard change would be necessary. He said private companies are effectively encouraged to act out of fear that an attack could affect share prices. He said simple fixes, like adding concrete walls rather than chain-link fences, could be a major step forward.
“We’ve got to trust that these actors know what they need to do to protect their systems,” he said. “Standards are a part of it, but they’re not the end all be all.”